What is a crypto scam? Explained with top scams to avoid in 2024
Crypto scams refer to any fraudulent practice in the cryptocurrency space aimed at tricking individuals into investing or giving away assets or …
Whilst regulators and law enforcement agencies focus their attention on ransomware, often the very same criminal syndicates are behind surging Business Email Compromise (BEC) attacks. In this blog, we will explore new evidence that attackers are shifting gear from ransomware to BEC and why every organisation needs to implement security measures to protect itself from insider threats.
Due to the high-profile nature of recent ransomware attacks, public attention has naturally focused on how to prevent becoming a victim.
But here are some statistics based on reports to the FBI that should concern you:
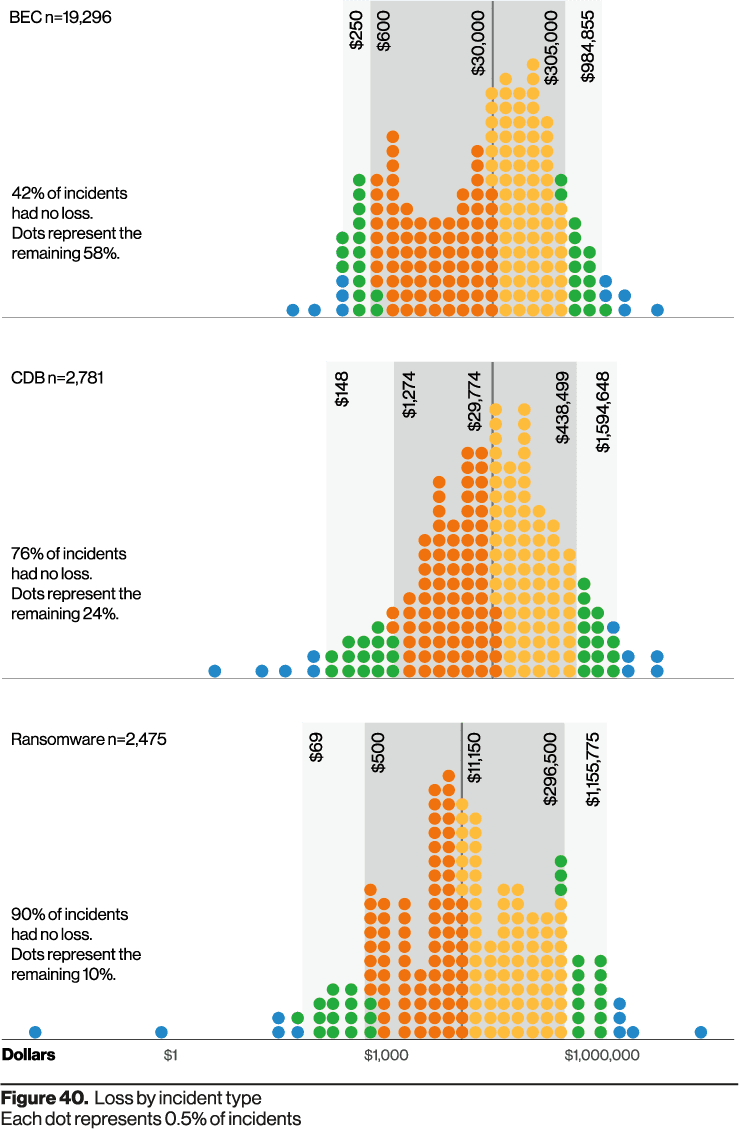
This diagram from the Verizon 2021 Data Breach Investigations Report, illustrates losses from three types of attacks: BEC, Computer Data Breach (CDB), and ransomware. Each dot represents half a percent of incidents.
As you can see, only 46% of BEC attacks did NOT result in losses. By contrast the vast majority of both CDB and ransomware attacks (76% and 90% respectively) did not result in losses.
In other words, if your organisation is subjected to a BEC attack, there is a far greater likelihood of you experiencing losses, compared to either CDB or ransomware attacks.
The message is clear – you really need to be paying more attention to the risks of BEC losses!
Another important take-away is that the number of BEC attacks is far greater than the number of either CDB or ransomware attacks:
Yet again, the risk of you facing a BEC attack is notably higher than other types of attacks.
If the fact you are more likely to face a successful BEC attack isn’t concerning enough, the financial losses should definitely keep you awake at night.
The median loss from each type of attack is:
All these facts should dispel any notion that your organisation can focus solely on stopping ransomware, whilst ignoring the threat of BEC.
New evidence is emerging of the intersection of ransomware and BEC attacks.
Researchers in the United States recently identified attempts by a Nigerian-based scammer to entice employees at a number of organisations to infect their corporate networks with ransomware. If they successfully installed the ransomware on either a company computer or a Windows server, the employee would be paid either $1 million in bitcoin, or 40% of the presumed $2.5 million ransom.
What makes this incident unique is that the attacker had initially sought to deceive the targeted employees via the usual BEC tactics. These typically include social engineering by collecting publicly-available contact details (usually via LinkedIn) and then sending them phishing emails. The scammers hope to obtain login and password credentials so they can access email accounts to carry out BEC attacks.
However, when the scammers were unsuccessful in their phishing attempts, they changed tactics and sought to recruit the employees into cooperating with a ransomware attack.
This case clearly demonstrates that often the same criminal syndicates are behind both attack methods and that insider threats may be putting your organisation at risk.
Insider threats may be a real danger to your organisation. In many cases, they also represent the hardest threats to identify and block. The reality is that every organisation needs grant employees access to a range of systems so they can perform their work duties.
Given the scale of BEC attacks and the heightened risk posed by insider threats, your organisation needs systems in place that will reduce the chances of experiencing severe financial losses. By integrating eftsure into your Accounts Payable processes, you will be able to maintain a comprehensive audit trail of outgoing payments. You will also be able to ensure that only legitimate invoices are paid and that the funds are only remitted to legitimate suppliers.
This gives you both visibility and confidence to reduce the risk that insider threats are defrauding your organisation.
Contact eftsure today for a no-obligation demonstration of how we can help your organisation protect itself from growing insider threats.
Crypto scams refer to any fraudulent practice in the cryptocurrency space aimed at tricking individuals into investing or giving away assets or …
A very real cyber risk lies within your business. Find out what you need to be aware of and how you can minimise insider threat risks.
The AT&T data breach impacts millions of customers and has exposed a trove of sensitive details. Here’s why that matters for finance leaders.
End-to-end B2B payment protection software to mitigate the risk of payment error, fraud and cyber-crime.